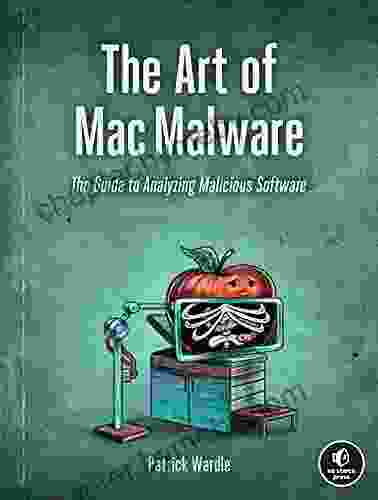
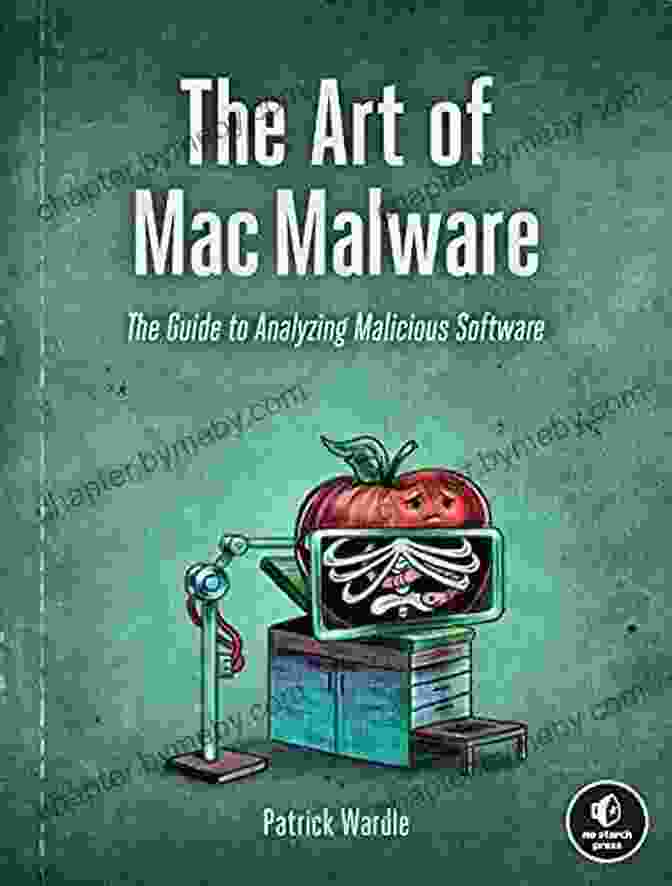
Unveiling the Secrets of Malicious Software: A Comprehensive Guide to Analysis

In the ever-evolving digital landscape, malicious software (malware) poses a significant threat to businesses and individuals alike. With the proliferation of sophisticated cyberattacks, it is essential to have a deep understanding of malware analysis techniques to protect critical systems and data.
Introducing "The Guide to Analyzing Malicious Software" — the ultimate resource for security professionals, researchers, and anyone looking to master the art of malware analysis.
4.7 out of 5
| Language | : | English |
| File size | : | 1655 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 462 pages |
This comprehensive and highly detailed book provides an in-depth examination of the various techniques employed to analyze malware, empowering you to effectively identify, understand, and counter these malicious threats.
Exploring the Depths of Malware Analysis
Embark on a journey into the enigmatic world of malware analysis as the book meticulously guides you through:
- The fundamental concepts of malware, its types, and its impact on systems
- Advanced static and dynamic analysis techniques to uncover concealed threats
- Practical approaches to reverse engineering and unpacking malware to reveal its inner workings
li>Forensic investigations and threat intelligence analysis to trace the origins and motives behind malware attacks
Exceptional Features for Enhanced Learning
The Guide To Analyzing Malicious Software stands out with its exceptional features, designed to enhance your learning experience:
- Real-world case studies: Examine real-life examples of malware attacks to gain practical insights into their analysis and mitigation
- Interactive exercises and labs: Engage in hands-on exercises and lab scenarios to reinforce your knowledge and hone your skills
- Industry expert contributions: Benefit from the wisdom and experience of leading security experts in the field
- Comprehensive glossary: Quickly reference key terms and concepts encountered throughout the book
Benefits for Security Professionals
By mastering the techniques outlined in this guide, security professionals can:
- Effectively identify and characterize malware threats
- Develop targeted and tailored defense mechanisms against cyberattacks
- Conduct thorough forensic investigations to trace the origins of malware
- Stay up-to-date with the latest malware analysis techniques and advancements
A Proven Resource for Cybersecurity Education
"The Guide to Analyzing Malicious Software" has established itself as a trusted resource for cybersecurity education and training. Universities, security academies, and training organizations worldwide utilize this book to equip their students and professionals with the necessary skills and knowledge to combat malware threats.
Reviews from educators and industry experts alike praise the book for its comprehensive coverage, clarity, and practical approach:
"An essential guide for anyone involved in the cybersecurity field. The detailed explanations and practical exercises provide a solid foundation for understanding and analyzing malware."
"A must-have reference for security professionals. This book empowers analysts with the knowledge and techniques to effectively identify, investigate, and mitigate malware threats."
Acquire Your Copy Today
Invest in your cybersecurity expertise and protect your digital assets and systems from malicious software. Free Download your copy of "The Guide to Analyzing Malicious Software" today and embark on a journey to master the art of malware analysis.
Available in both print and digital formats, this essential guide is accessible to security professionals, researchers, students, and anyone looking to enhance their understanding of malware analysis.
Secure your copy now and elevate your cybersecurity knowledge to the next level.
Free Download Your Copy
4.7 out of 5
| Language | : | English |
| File size | : | 1655 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 462 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Stefano Mastrogiacomo
Stefano Mastrogiacomo Michael Zuber
Michael Zuber Michael Cave
Michael Cave Sabrina Snyder
Sabrina Snyder Pat Garber
Pat Garber Susan Niermeyer
Susan Niermeyer Matthew Vanfossan
Matthew Vanfossan Meghan Leahy
Meghan Leahy Michelle Kadarusman
Michelle Kadarusman Matt Picheny
Matt Picheny Mike Watt
Mike Watt Richard D Sawyer
Richard D Sawyer Michael Massing
Michael Massing Michael Collins
Michael Collins Nick Mehta
Nick Mehta Melinda Hardin
Melinda Hardin Mick Herron
Mick Herron Michael Martin
Michael Martin Stefan Jansen
Stefan Jansen Marsha Graham
Marsha Graham
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Fernando PessoaUnearthing the Timeless Tale of Artistic Rivalry and Divine Wrath: Exploring...
Fernando PessoaUnearthing the Timeless Tale of Artistic Rivalry and Divine Wrath: Exploring...
 Douglas FosterThe Untold Story of Scipio Jones and the Battle to Save Twelve Innocent Men
Douglas FosterThe Untold Story of Scipio Jones and the Battle to Save Twelve Innocent Men Jeremy MitchellFollow ·3.1k
Jeremy MitchellFollow ·3.1k Charlie ScottFollow ·12.8k
Charlie ScottFollow ·12.8k W.H. AudenFollow ·9.9k
W.H. AudenFollow ·9.9k Demetrius CarterFollow ·4.2k
Demetrius CarterFollow ·4.2k Harry HayesFollow ·8.6k
Harry HayesFollow ·8.6k Fabian MitchellFollow ·11.3k
Fabian MitchellFollow ·11.3k Jaden CoxFollow ·4k
Jaden CoxFollow ·4k Brent FosterFollow ·15.9k
Brent FosterFollow ·15.9k
 Henry James
Henry JamesCold War Fighter Pilot Story: A Captivating Tale of...
Enter the Cockpit of...
 Rudyard Kipling
Rudyard KiplingYour Body Your Baby Your Choices: The Essential Guide to...
Pregnancy and...

 Fabian Mitchell
Fabian MitchellMichelle Obama: An Intimate Portrait - A Must-Read for...
Michelle Obama is a prominent figure in...
 Juan Butler
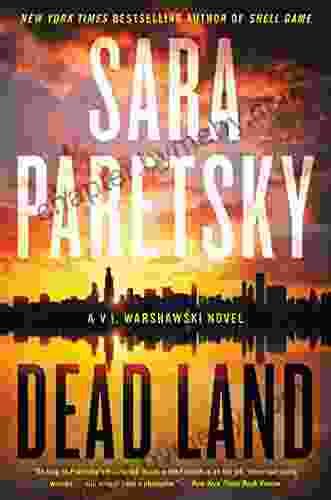
Juan ButlerUncover the Secrets of the Dead Land Warshawski Novels
Prepare to delve...
4.7 out of 5
| Language | : | English |
| File size | : | 1655 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 462 pages |